List of TCP and UDP port numbers
List of TCP and UDP port numbers from 0 to 1023
This is a list of Internet socket port numbers used by protocols of Transport Layer of the Internet Protocol Suite for the establishment of host-to-host connectivity.
Originally, port numbers were used by the Network Control Program (NCP) which needed two ports for half duplex transmission. Later, Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) needed only one port for bidirectional traffic (full duplex). The even-numbered ports were not used, and this resulted in some even numbers in the well-known port number range being unassigned. Stream Control Transmission Protocol (SCTP) and Datagram Congestion Control Protocol (DCCP) also use port numbers. They usually use port numbers that match the services of the corresponding TCP or UDP implementation, if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[1] However, many unofficial uses of both well-known and registered port numbers occur in practice.
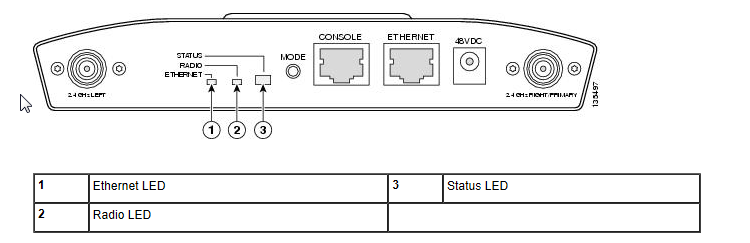
Cisco Access Point LED Status
Cisco Access Point LED Status
Checking the Lightweight Access Point LEDs
If your lightweight access point is not working proberly, you can check the Status, Ehternet, and Radio LEDs.
To see quickly the LED status and there meanings, use the following table to get a brief overview.
Understanding Cisco Access Point IOS Images
Understanding Cisco Access Point IOS Images
Introduction
All Cisco Aironet wireless access points and bridges were shipped in general with an IOS Software.
The only exception is the OEAP602.
Note:Some older Cisco access points did not run IOS, such as the Aironet 340 which ran only VxWorks, and the 1000 series lightweight APs.
Access Point IOS is distributed as a tar file. These tar files can be downloaded from cisco.com SDS; lightweight IOS images (k9w8) are also bundled in
the WLC software images (.aes). The IOS image names include the following components. Continue Reading →
Repair a corrupted IOS Image on a LWAPP
Repair a corrupted IOS Image on a LWAPP
Introduction
Here i would like to describe, how to set an access point to factory default.
My prefered manner is to formatting the flash of an access point,
copy the IOS Image from a tftp server and extract the tar file.
You need to execute some special command to extract the tar file.
If you copy only the tar file to the flash, it doesn’t work and the access point are not able to boot from the image. Continue Reading →
Wireshark display filters
Wireshark general
Wireshark is a free and open-source packet analyzer. This tool is used for network troubleshooting, analysis,
communication and software protocol development and education. The original software were named Ehtereal, in May 2006.
Later it was renamed to Wireshark due to trademark issues.
Wireshark uses pcap to capture packets. It runs on several platforms like GNU/Linux, OS X, BSD, Solaris,
some other Unix-like operating systems, and Microsoft Windows.
There is also a terminal-based version (non-GUI) called TShark.
Here I’d like to introduce some important filter options in wireshark.
It’s very hard to find exactly the right packets, you are looking for, in a hugh amount of data.
The following charts are a compendium of several websites.
My aim for these post was, to bring the most important commands of one page.
&nb
Wireshark Homepage
Understanding VLAN Trunk Protocol
Understanding VLAN Trunk Protocol
1. Introduction
Vlan Trunk Protocol (VTP) reduces administrative effort in a switched network.
There are 3 different types of vtp operating modes.
- Server
- Client
- Transparent
IOS Recovery from corrupt or missing image from ROMMON
IOS Recovery from corrupt or missing image from ROMMON
Indrodution:
hereby i describe how to recover from a corrupt or missing software image on
a Cisco Catalyst switch 2900XL and 3500XL. I will show you the steps and 2 examples to load
a software image with the hyperterminal software ‘tera term’ or ‘SecureCRT’.
default interface nexus 5000
default interface nexus 5000 tcl script
In my latest post i wrote something about vpc double sided configuration with N5k.
Due to of refinishing i have to define several ports on the n5k device as port-channels or as
access-ports. This ports are used in previous environment for different purposes on the
N5k devices.
Continue Reading →
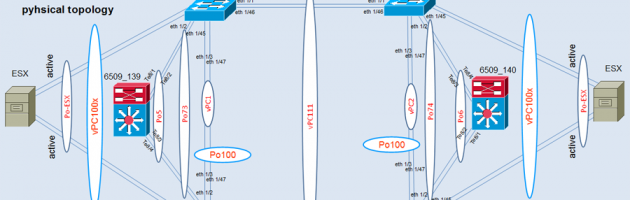
Double-Sided vPC with N5k and Cat6500
Double-Sided vPC with N5k and Cat6500
1. Introduction
Here i want to explain, how to create a double-sided vpc in an enterprise environment.
A customer of us want to redeploy his ESX Server connection from active-passive to active-active.
In the past the ESX Server were single-sided connected to one of the N5k devices with two 10 Gbit links.
The ESX Server were bundled in a port-channel on both sides. (N5k <-> ESX)
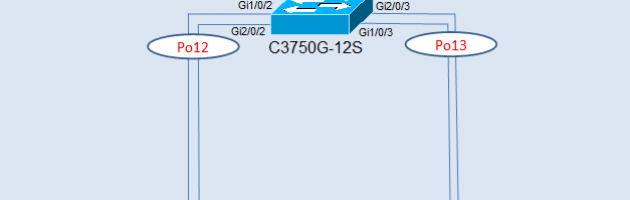
DHCP Discover Failure in a Port-Channel
DHCP Discover Failure in a Port-Channel
1. Introduction
Yesterday we stumbled over an absolutely curious phenomenon in association with the DHCP
process and a port-channel. With a port-channel the DHCP discovery process fails.
Our network design is like cisco enterprise environment commended. There are an
access-layer -> distribution layer -> core layer (in direction to the core).
Everything works fine from the beginning from SW1 and SW2. DHCP discovery is
no problem and works fine. On switch 1-3 we have dhcp snooping operational.
The dhcp snooping trust settings are set to the uplinks and respectively to the port-channels.
Recent Network Posts
Network-Categories
- ASA 5505 (1)
- Basics (10)
- Data Link Layer (4)
- Layer 2 Features (3)
- Network Layer (1)
- Nexus Datacenter (2)
- Physical Layer (1)
- Transport Layer (1)
- WLC (4)
Network-Calendar
| M | T | W | T | F | S | S |
|---|---|---|---|---|---|---|
| « Nov | ||||||
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 | |||||
Information
Network-Categories
Blog Traffic
- Visits Today: 907
- Total Visits: 177733
- Total Visitors: 14
- Total Countries: 1911