Now i want to show how to configure a IPSec Remote-Access with an ASA5505.
Given is a DSL-Modem(NTBBA) and an ASA5505 with a Software Image <=8.3.
1. Prepare the ASA for the WAN connection.
In this section you learn how to configure the ASA5505 to get a connection to the WAN.
We used the Interface Vlan1 to connect with the DSL-Modem. Please set the DSL-Modem to
‘Pass-through Mode’.
- At this point you can reach the ASA5505 with the external IP address from your provider
The following steps will grant IPSec Remote access
Step 1. Enable ISAKMP
Step 2. Create ISAKMP policy
- Priority = a number between 1 and 65535.
ISAKMP begins with the lowest number. Is there no match – then the very next higher number will match and so on… - Encryption = choose the appropriate encryption type. The following types are available: 3des;aes(128bit);aes-192;aes-256;des
- Hash = you can choose between MD5 and SHA.This check the paket on the way of transport (if the paket changed on the way of delivery) = Data Integrity
- Authentication = you can choose between preshared keys;CRACK;RSA. A mechanism to handle the identity of the remote peer
- D-H Group = allocation of a preshared key between 2 VPN devices. IKE policies support Group 1,2,5,7. In a normal case you choose Group 2 or 5.
- Lifetime = Lifetime of a ISKAMP key. In normal case the lifetime is 86400 sec.
Step 3. Set up tunnel and group policies
- Addition = Cisco ASA uses a ‘inheritance model’ to push network and security policies to the enduser. Possible locations are: default group policy; user’s assigned group policy; specific user’s policy. There are a default policy called DfltGrpPolicy (System Default). If a new policy is created, this will be applied under the ‘User Group Policies’.
These Policies can be configured specially. Otherwise the properties of the DfltGrpPolicy will be inherit.
Step 4. Define IPSec policy
- Set Name = decribe the name of the transformset. The name has only local meaning and it’s not important for the tunnel establishment respectively transfer
- ESP Encryption = there are several encryption types. esp-3des; esp-aes (128bit); esp-aes-192; esp-aes-256; esp-des; esp-none; esp-null
- ESP Authentication = you can choose between MD5 and SHA.esp-md5-hmac (esp md5 authentication);esp-sha-hmac (esp sha authentication)
- Mode = here you can choose between ‘Tunnel’ and ‘Transport Mode’.
Transport Mode encrypt and authenticate the data packets between the VPN peers. Tunnel Mode encrypt and authenticate the IP packets between the VPN peers. In a remote access connection usually the Tunnel Mode will be used.
Step 5. Configure user authentication
Well known cisco user authentication.
Step 6. assign an IP address
Mapping an address pool to the GroupPolicy
Step 7. Create a crypto map
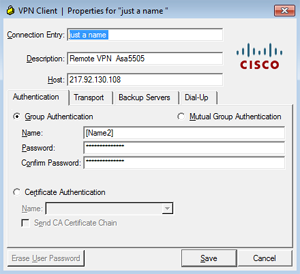
Step 8. configure the VPN Client
Now you have to put in the Group Authentication from step 3. in the following fields.
1. Connection entry: just a name
2. Description: this speaks for itself
3. Host: the external WAN IP address, with which you are reach the ASA5505 .
Radio Buttion -> Group Authentication
Name: [Name2] and password
1. Connection entry: just a name
2. Description: this speaks for itself
3. Host: the external WAN IP address, with which you are reach the ASA5505 .
Radio Buttion -> Group Authentication
Name: [Name2] and password
The final prepare is to set the transport tab like shown
on the image.
on the image.





Hi there,I’m having tuborle connecting to Vypr through my recently installed ASA5505. This is the ONLY site I can find with any info on setting this up through ASDM, so thanks!I’ve followed your steps and have the two access rules in place and have enabled the IPSEC Pass Thru Rule Action under Global Policy Inspection Rule.When I try to connect, the link *appears* to establish, but when checking Username & Password (I’m using the simple Windows VPN connection, not the Vypr client), the ASA log reports: regular translation creation failed for protocol 47 src inside:10.xxx.xxx.xxx dst outside:216.yyy.yyy.yyy Any ideas, what might be missing?Cheers,I.
Hi Rajesh,
please use the VPN Client from Cisco. I never try a VPN Client
from another vendor. I’m not sure if Vypr works fine with Cisco.
Kind Regards
George